Table of Contents
Most traditional tech career paths are facing massive shifts due to automation. A standard junior developer or entry-level graphic designer is finding the market incredibly tight, as simple coding tasks and stock visual creation are increasingly offloaded to smart algorithms. If you plan to build a long-term, high-income tech career, you cannot afford to build your foundation on easily automated skills.
This brings us to a critical question: Is cybersecurity still worth studying in 2026?
The short answer is yes, but the way you enter the market has completely changed. Organizations don’t just need people to check logs or configure basic firewalls anymore. With AI-driven cyber threats rising, the tech world needs specialized practitioners who can build secure architecture and actively defend complex infrastructure.
Let’s break down the real state of cybersecurity career paths, global and local salary realities, the impact of AI, and the exact steps to go from zero to your first high-ticket remote or local contract.
1. The Global & Local Threat Landscape in 2026

To understand why this field is growing, look at what businesses are dealing with daily. As small and large corporations migrate their databases to the cloud, their attack surface expands significantly.
In the local Kenyan ecosystem, the expansion of mobile money infrastructures, digital banking API integrations, and e-commerce growth has made small and medium enterprises (SMEs) highly attractive targets for malicious actors. A single data breach or a sustained Distributed Denial of Service (DDoS) attack can wipe out an online storefront’s entire quarterly revenue.
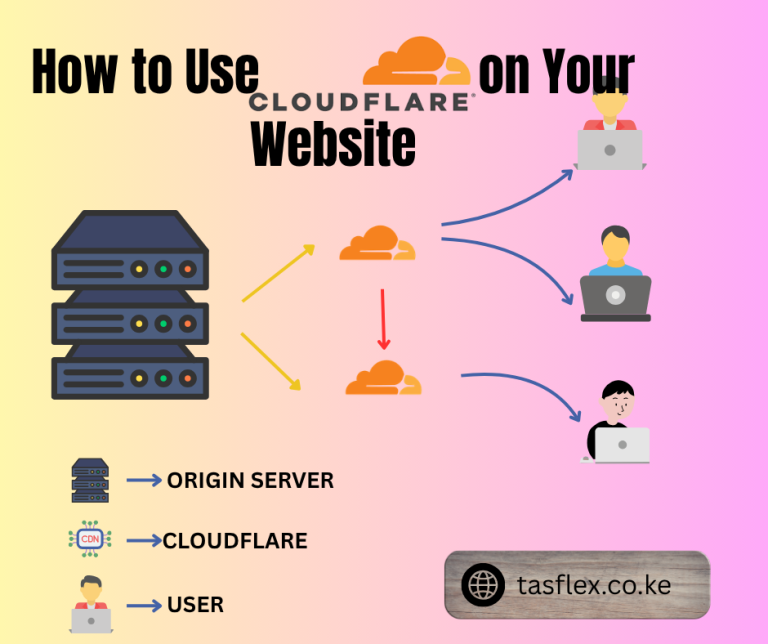
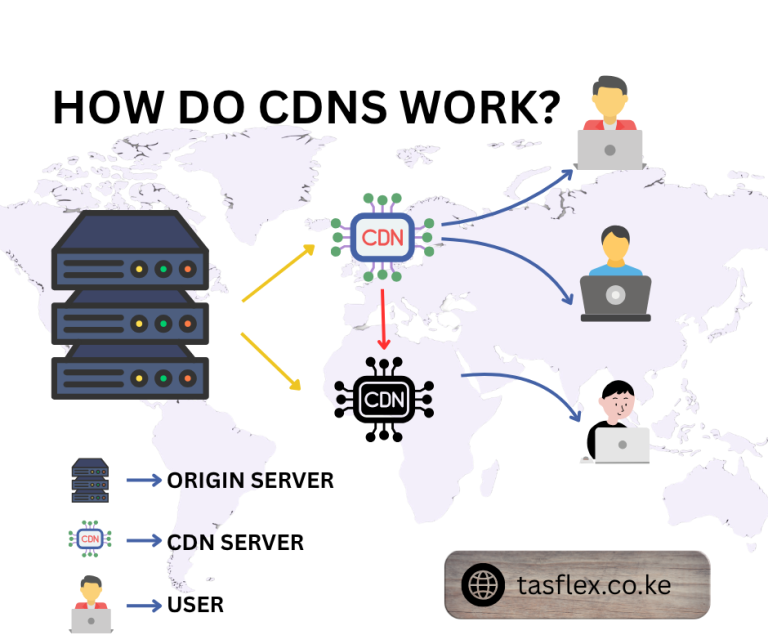
Because of this risk, proactive protection is no longer just a concern for major banks or telecommunication companies. Even local businesses setting up digital real estate require an understanding of security basics, such as moving away from raw hosting configurations toward secure implementations using a proxy or a Content Delivery Network (CDN). The demand for security infrastructure has trickled down to every corner of the web.
2. Core Career Paths in Cybersecurity
Cybersecurity is not a single job; it is a collection of highly distinct, specialized domains. Understanding these branches will help you decide where to focus your study time.
A. Offensive Security (The Red Team)

- What it is: Ethical Hacking and Penetration Testing. Your job is to think like a malicious actor, discover vulnerabilities in a client’s application or network before real attackers do, and provide a clear roadmap to fix them.
- The Day-to-Day: Running vulnerability scans, writing custom scripts to exploit security gaps, and performing social engineering tests.
B. Defensive Security (The Blue Team)

- What it is: Security Operations and Incident Response. Your job is to monitor a company’s infrastructure, detect unauthorized access patterns, and immediately isolate compromised servers to minimize damage.
- The Day-to-Day: Managing Security Information and Event Management (SIEM) dashboards, analyzing suspicious network traffic, and strengthening access control configurations.
C. Application & Cloud Security (The DevSecOps Pipeline)
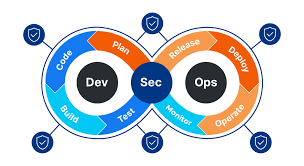
- What it is: Ensuring code is built securely from day one. Instead of scanning a finished product for flaws, Application Security engineers embed automated security checks directly into the software development workflow.
- The Day-to-Day: Auditing code repositories, managing API authentication keys, and securing cloud environments (AWS, Google Cloud, Azure).
3. The Financial Reality Check: Salaries & Rates

If you want to earn a premium living in this industry, your goal should be to position your skills to capture international remote work or serve high-tier local corporate sectors.
The Remote / Freelance USD Market
Cybersecurity is one of the highest-paying digital skills because the stakes are high. If a business loses customer credit card data, they face massive fines and legal crises. When you prevent that, you can charge premium prices for your advisory or engineering work.
On freelance platforms like Upwork and Fiverr, specialized security consultants command high rates:
- Vulnerability Assessments for SMEs: $500 – $1,500 per project.
- Hourly Consulting Rates: $50 – $150+ per hour depending on technical focus.
- Monthly Infrastructure Retainers: $2,000 – $5,000+ per month for ongoing cloud monitoring.
For strategies on how to position yourself for these contracts, check out our guide on the best freelance skills to start on Fiverr and Upwork.
The Kenyan Corporate Market
Locally, banks, fintech startups, government agencies, and telecom firms are competing heavily for top-tier defense talent.
- Entry-Level (Associate Analyst): KSh 70,000 – KSh 120,000 per month.
- Mid-Level (Penetration Tester / SecOps Engineer): KSh 180,000 – KSh 350,000 per month.
- Senior Roles (CISO / Principal Architect): KSh 500,000 – KSh 1,000,000+ per month.
4. Will AI Replace Cybersecurity Professionals?
A common fear among prospective students is that artificial intelligence will automate cybersecurity entirely. The reality is the opposite: AI is amplifying the need for skilled human practitioners.
While AI can scan lines of code for known patterns faster than a human, it lacks the context, strategic intuition, and creative problem-solving needed to counter complex, multi-stage human attacks. AI tools are becoming part of the modern security toolkit, used to parse millions of log data points instantly, but a human operator must still interpret the results, make the final architectural decisions, and lead incident responses.
The professionals who survive and thrive are those who use AI to work faster, leaving the low-value repetitive tasks behind to focus entirely on high-level strategy and system validation.
5. The Seing Dust Phase: What It Takes to Start From Zero
Let’s be completely realistic: No one walks into a high-paying cybersecurity role after watching a few YouTube tutorials. This is a highly technical discipline that requires pushing through an initial slow period where you must build your practical competence from scratch.
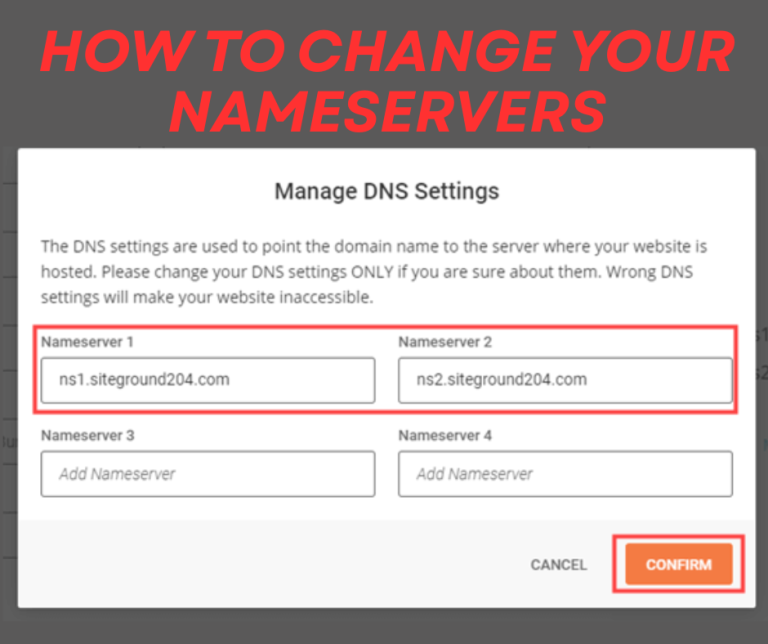
You will have to spend months understanding how networks communicate, how operating systems manage memory, and how data moves securely across the web. You will practice configuring firewalls, analyzing raw packet captures, and setting up proxy layers, much like the deep DNS management required when you connect a domain to Cloudflare to secure it from malicious traffic.
The Learning Roadmap
Phase 1: Foundations (Months 1-3)
----------------------------------
- Master Networking Essentials (TCP/IP, DNS, OSI Model)
- Learn Linux Command Line & Basic Scripting (Python or Bash)
- Understand Web Architecture & HTTP Protocols
Phase 2: Practical Application (Months 4-6)
--------------------------------------------
- Build local lab environments to test vulnerabilities
- Practice on interactive platforms (TryHackMe, HackTheBox)
- Earn foundational, globally-recognized certifications
Phase 3: Portfolio & Outreach (Months 7+)
------------------------------------------
- Document your technical process via write-ups or case studies
- Set up a professional digital portfolio website
- Apply for entry gsplitting tasks or freelance consultations
6. Essential Tools of the Trade
To study effectively, you need to become fluent in the industry-standard software suites used by security professionals globally.
| Tool Name | Core Purpose | Specialized Function |
| Wireshark | Network Traffic Analysis | Captures and analyzes live data packets moving across a network. |
| Burp Suite | Web Application Auditing | Acts as an intercepting proxy to test web application security configurations. |
| Nmap | Network Discovery & Scanning | Maps out network architecture and identifies active ports and services. |
| Metasploit | Penetration Testing Framework | Validates discovered vulnerabilities using a library of known exploits. |
| Linux (Kali / Parrot) | Dedicated Security OS | Operating systems packed with pre-installed tools for advanced testing. |
To run these virtualization environments smoothly, ensure your hardware matches the computational demands. Review our checklist of the best laptops and tools for digital professionals.
7. How to Land Your First $100 and Build Long-Term Authority
The biggest hurdle for new cyber professionals is a lack of commercial experience. To bypass this, you must treat your knowledge as a product and display your skills publicly.
Step 1: Create a Practical Portfolio
Do not rely on a standard, text-heavy resume. Build an online presence that displays your projects, lab configurations, and security write-ups. If you don’t show your work on your own domain, clients have no reason to trust your technical capability.
Learn how to construct an authoritative digital showcase in our guide on how to build a professional portfolio in Kenya.
Step 2: Pitch the Micro-Audit
When applying for freelance contracts on platforms like Upwork, don’t pitch a massive, expensive security overall immediately. Offer a low-risk, tightly scoped entry point, such as a WordPress security review, an SSL configuration audit, or a basic vulnerability scan.
For step-by-step guidance on winning your initial contracts, refer to our guide on securing your first $100 on Upwork and Fiverr.
Step 3: Write Detailed Case Studies
Whenever you solve a security problem or complete a difficult laboratory challenge, document the process cleanly. Use the STAR method (Situation, Task, Action, Result) to explain the problem you faced and how your technical intervention secured the asset.
Frequently Asked Questions (FAQs)
1. Do I need a computer science degree to get a cybersecurity job?
No. While a degree can help clear corporate HR filters, the modern freelance and remote tech markets prioritize demonstrated technical competence. Your portfolio of documented case studies, lab certifications, and practical knowledge acts as your real resume.
2. Which certification should a complete beginner start with?
The CompTIA Security+ is the globally recognized baseline certification for entering the industry. If you want a purely practical, hands-on offensive entry point, look into the EJPT (Junior Penetration Tester) certification.
3. Can I practice cybersecurity on a standard consumer laptop?
You can start learning on a mid-range laptop (Core i5 or Ryzen 5 with 8GB RAM), but as you begin running multiple virtual machines simultaneously to simulate networks, you will need to upgrade to at least 16GB of RAM and fast SSD storage.
4. What is the difference between cybersecurity and software engineering?
A software engineer focuses on building systems, applications, and features to meet business requirements. A cybersecurity professional focuses on analyzing those systems to find structural flaws, defend them from attacks, and ensure data integrity.
5. How long does it take to become employable?
If you dedicate 2 to 3 hours of focused, daily study to practical labs and foundational concepts, you can build enough technical competence to secure entry-level freelance consultations or junior security roles within 6 to 9 months.
Build Secure Foundations for Long-Term Growth.
Cybersecurity is an demanding but highly rewarding discipline that offers a powerful hedge against automation. If you are ready to stop chasing temporary digital trends and build deep, technical equity, the security space is a viable path forward.
Explore our high-performance technical and branding services and let’s position your business or portfolio for long-term growth